Digital data moves between devices every day. It travels across servers and networks. People share files by email and cloud storage. They also use messaging apps. Software updates come from the internet. During these actions, files can get corrupted. They can also be changed without notice. That is why many people ask what is Hash integrity and how it protects important information.
Hash integrity checks if data stays the same. It creates a unique code from the file content. This code is called a hash value. Even a tiny change will create a new code. Many users also look up what is hashing data integrity. They want to confirm that their files are safe and complete.Integrity checks are useful for everyone.
Try Recoverit to Recover Lost Data
Security Verified. Over 7,302,189 people have downloaded it.
Table of Contents
Part 1: What is Hash Integrity?

Many beginners want to clearly understand what is Hash integrity before using technical tools. In simple terms, hash integrity is a process used to confirm that digital data has not changed. A mathematical formula converts the original file into a fixed-length string of characters. This string is known as the hash value.
The important point is that the hash value represents the exact content of the file at a specific moment. If the file changes in any way, even by adding or removing a single letter, the generated hash will also change completely. This makes hash integrity an effective way to detect unwanted modifications.
When users ask what is hashing data integrity, they are referring to the same concept. Hashing transforms data into a digital fingerprint. This fingerprint can later be compared with a new hash to ensure the file is still original.
Hash integrity does not depend on file size. A small text file and a large video file both produce hash values of fixed length when using the same algorithm. This consistency makes the system practical and efficient for many uses.
Part 2: How Hash Integrity Works?
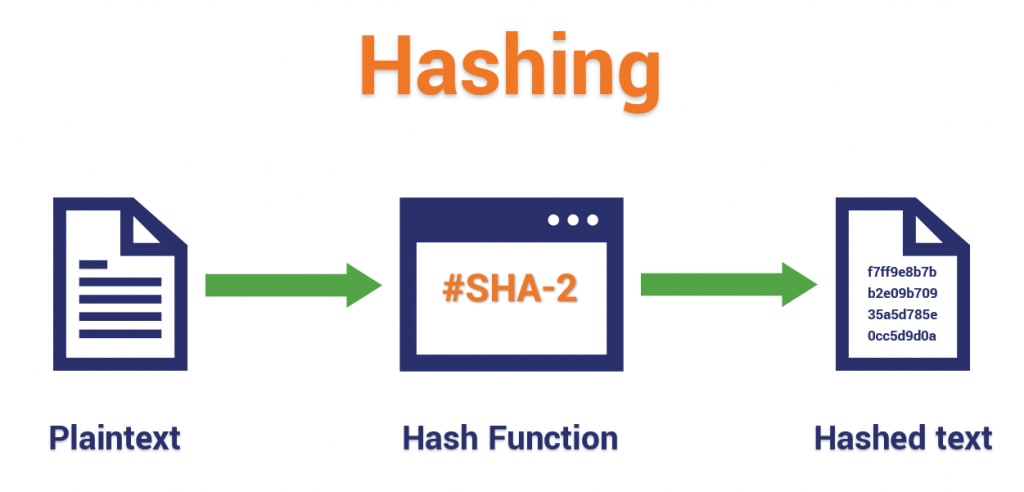
To understand what is hashing and how does it work, it is helpful to look at the process step by step. A hash function takes input data and performs a series of calculations. It then produces a unique string of characters. This output always has the same length when using a specific algorithm.
For example, if you apply a hash function to a document today, you will receive a hash value. If you run the same function on the same file tomorrow, the hash will be identical. However, if even one character is changed, the output will be entirely different. This behavior makes hashing reliable for integrity checks.
Many people also ask how does a hash function ensures data integrity. The answer lies in sensitivity. Hash functions are designed so that even the smallest input change produces a completely different result. This property is called the avalanche effect. It makes it nearly impossible to modify a file without detection.
When verifying a file, users generate a new hash and compare it with the original published value. If both values match, the file remains unchanged. This comparison process explains how to check hash integrity in practical situations such as downloads or backups.
Part 3: Why Hash Integrity Matters in Modern Security?

Hash integrity plays a central role in protecting digital information across different industries. As data volumes grow, simple and reliable verification methods become essential.
- Detects file tampering: If an attacker edits a file, the hash changes immediately. This allows fast identification of unauthorized modifications.
- Protects software downloads: Developers often publish hash values with their software. Users compare these values to confirm safe installation.
- Supports secure communication: Emails and shared documents can be verified to ensure no hidden changes occurred during transfer.
- Ensures backup accuracy: Organizations use hashing to confirm backup copies are exact duplicates of original files.
- Secures financial records: Banks and financial institutions use hashing to protect transaction logs from silent manipulation.
- Helps with password storage: Passwords are converted into hashes before storage. This reduces exposure of plain text credentials.
- Prevents unnoticed corruption: Hardware failures can damage files. Hash comparison reveals such corruption quickly.
- Works with strong algorithms: Security teams often evaluate what is the best hash for integrity before choosing an algorithm like SHA-256.
Hash integrity supports trust in digital systems. Without it, detecting hidden changes would be difficult and time-consuming.
Part 4: Real-World Uses of Hash Integrity
Hash integrity is widely used beyond cybersecurity teams. It supports everyday digital operations across different sectors.
- Software distribution: Operating systems and applications provide hash values for verification after download.
- Cloud storage services: Cloud systems calculate hashes to maintain data consistency across servers.
- Email attachments: Organizations verify attachments to ensure documents arrive without modification.
- Blockchain networks: Each block contains a hash linked to the previous block, creating secure chains.
- Digital forensics: Investigators calculate hashes to prove digital evidence has not been altered.
- Operating system updates: Before installation, systems confirm update files match official hash values.
- File synchronization tools: Sync programs use hashes to detect changes between devices.
- Data migration projects: During server transfers, IT teams rely on hashing to verify accuracy.
Understanding what is hashing data integrity helps users see why hashing is trusted in these practical examples.
Part 5: Key Benefits of Hash Integrity
Hash integrity provides clear advantages for individuals and organizations managing digital data.
- Simple comparison process: Checking two hash values takes very little time.
- Fast performance: Modern hash algorithms process large files efficiently.
- Fixed-length output: No matter the file size, the output length remains consistent.
- Sensitive change detection: Even small changes produce noticeably different hash values.
- Automation friendly: Systems can schedule automatic hash checks for important data.
- Flexible algorithm choice: Security teams can evaluate what is the best hash for integrity based on risk level.
- Strengthens user confidence: Verified files build trust among customers and partners.
- Reduces malware risk: Unauthorized modification often changes hash values, signaling possible threats.
When users learn what hashing is and how it works, they recognize why it is widely adopted in secure systems.
Part 6: Limits and Challenges of Hash Integrity

Although hash integrity is powerful, it also has certain limitations that users must understand.
- Cannot repair corrupted files: It only detects changes. It does not restore damaged data.
- Possibility of collisions: Two different inputs may rarely produce the same hash.
- Weak algorithms exist: Older methods, such as MD5, are no longer considered secure.
- Requires secure hash sharing: If attackers alter the original published hash, verification becomes useless.
- Detects but does not block attacks: Additional security tools are needed for prevention.
- Requires correct user action: Users must understand how to check hash integrity properly.
- Large-scale monitoring can be complex: Managing thousands of file hashes demands structured systems.
- Must be combined with other controls: Encryption, backups, and access management remain necessary.
When discussing how a hash function ensures data integrity, it is important to note that hashing works best as part of a broader security strategy.
Part 7: Hash Integrity Checks Failed? Recoverit Can Help Restore Lost or Corrupted Files
In some cases, hash verification reveals that a file has changed or become damaged. The file may fail to open. It may show unexpected errors. Users often feel frustrated when integrity checks fail, especially if the file is important.
Recoverit is a professional data recovery solution designed to restore lost, deleted, or corrupted files. If hash verification shows that data has been compromised, Recoverit scans storage devices to locate recoverable content. It works with hard drives, SSDs, USB drives, and memory cards.
The tool is useful when corruption results from power failures, improper transfers, or system crashes. Users who learn how to check hash integrity may discover problems early. Recoverit provides a practical solution when recovery is required.
3 Detailed Recovery Steps
Step 1. Select the Storage Location Open Recoverit and choose the drive or folder where the file was stored before corruption.

Step 2. Start the Scanning Process Allow the program to perform a complete scan. This may take time, depending on storage size.

Step 3. Preview and Restore Files Review the scan results. Select the required files and save them to a secure location.

Part 8: How to Implement Hash Integrity in Practice
To implement hash integrity, begin by choosing a strong and modern algorithm. Many professionals recommend SHA-256 when evaluating what the best hash for integrity is. Avoid outdated algorithms that have known weaknesses. After generating the original hash, store it in a secure and trusted location.
Whenever the file is transferred, copied, or downloaded again, generate a new hash using the same algorithm. Compare both values carefully. This process explains how to check hash integrity in daily workflows. By understanding what hashing is and how it works, individuals and organizations can build a reliable verification routine.
Automating this process through scripts or management tools can further improve consistency. Businesses often schedule regular integrity scans to detect unexpected changes early.
Conclusion
Hash integrity provides a dependable way to verify digital file authenticity. It creates a unique fingerprint that changes whenever data changes. When people ask what Hash integrity is, the core idea is simple. It ensures that information remains original and unmodified.
From personal downloads to enterprise systems, hash verification strengthens digital trust. Learning what hashing data integrity is and applying proper checks reduces risk and improves confidence in data security practices.
FAQs
-
What is Hash integrity in simple terms?
Hash integrity is a way to check that a digital file has not been altered or damaged. It works by creating a unique code called a hash value from the file’s content. This code acts like a digital fingerprint. If the file changes in any way, even slightly, the hash value will also change, which signals that the file is no longer the same as the original. -
What is the best hash for integrity verification?
SHA-256 is widely considered a strong and reliable choice for integrity verification. It offers high security and a very low chance of producing the same hash for different data. Because of its strength and stability, it is commonly used in software downloads, cybersecurity systems, and many modern digital platforms. -
How does a hash function ensure data integrity?
A hash function ensures data integrity by converting data into a fixed-length string of characters based on the exact content of the file. The process is highly sensitive to change, so even a minor edit produces a completely different result. By comparing the original hash with a newly generated one, users can quickly detect whether the data has been modified.











 ChatGPT
ChatGPT
 Perplexity
Perplexity
 Google AI Mode
Google AI Mode
 Grok
Grok






















