Alert USB Attack: Easy Ways to Prevent USB From Attacks
Did you know that a USB drive can be used to exploit all your personal information? If not then, you should know that nowadays, a USB attack can be as dangerous as someone robbing you at gunpoint.
You may not realize yet, but this is the case: a USB drive that started just as a file-sharing service has become a primary hacking source. The USB attacks are growing because of a lack of awareness of these attacks.
But how can one prevent USB attacks? To help you with that, this article will tell you what a USB attack is and how you can avoid a USB attack. In the end, and it will also share a simple way to deal with data loss due to USB attacks. If you want to avoid those USB Attacks as much as possible, then just scroll down.
Part 01: Overview of USB Attack

To understand how you can prevent the USB attack, you will first learn a USB attack in a true sense.
A USB attack is a way the hackers execute malicious software through the USB device or USB port. The malicious software can exploit your computer system for confidential information. Hackers using this information can blackmail you. To know more information about malware: Steps to Delete Malware/Viruses from Your Computer
Although it might seem scary, don't worry. After reading this article, you will have sufficient knowledge to protect yourself from these attacks.
1. Some Usual Types of USB Attacks
Before you proceed further, you need to know some commonly occurring types of USB attacks. Understanding the type of USB attack will help you identify if you face anything similar to that.
Below are the usual types of USB attacks:
- Reprogrammable Microcontrollers: The internal microcontroller of the USB device is reprogrammed. After that, it carries out keyboard operations. E.g., preloaded keyboard strokes are stored in the microcontroller. As you plug the USB in, the keystrokes are automatically executed.
- Firmware Attacks: The firmware software inside a USB device is programmed to perform malicious actions. E.g., downloading infected files automatically or executing malicious commands.
- Unprogrammed USB Attacks: In such attacks, the USB device might seem empty to you; but there can be hidden files inside of it. Such hidden files can be used to secretly carrying confidential data.
- Electrical USB Attacks: When you plug in the USB, they cause a high voltage electric surge. The purpose is to damage the devices connected with your computer system, even your motherboard.

2. How Does USB Get Attacked?
A USB can perform operations itself that can be harmful to your computer. But how does the USB itself get attacked in the first place?
A few of the ways are mentioned below:
- Accidentally Plugging USB into Harmful Devices: When you attach your USB device to any infected computer system, your USB can get infected too. So, when you inject the USB into your computer, the USB transfer the virus to your system as well.
- Intentionally Corrupting USB: Some hackers may deliberately copy threat files into a USB and hand them to you. When you plug that USB into your system, it starts to attack the whole system.
- Downloading Files from Unknown Sources: When you download files from untrusted sources and copy them into your USB, they infect the USB drive.
However, these were the common ways USB can get attacked, but you must know them to take any precautions against them.
3. The Threats of Being Attacked:

You must be wondering what potential damage a USB attack can do? To make you realize the severity, see the below list:
- When malicious software inside a USB is executed, it can give the whole system control to a hacker. The hacker can easily steal any information through it.
- Hackers can also use USB attacks to secretly access your computer's webcam, keyboard, or even microphone.
- A USB attack can give hackers authority to delete data from your computer system.
- Hackers can also use the USB attack to damage the connected hardware to your system, making them unable to run and, in worse-case failing them.
Now that you have learned some fundamental knowledge of USB attack, let's move on to dig into the reasons why you should prevent these attacks.
Part 02: How to Prevent USB Attack?
Indeed, you have built some understanding of USB attacks by now. How they come in the first place, and what threats they offer to a computer user. The question is, "Are Your USB Devices Safe?" The answer is subjective, but Yes, in our opinion.
But don't worry, your ambiguities will all be cleared, and this section will jump straight to the tips that can help you prevent a USB attack. There have compiled a list of standard recommendations that can be helpful for you.
Tip 1: Use Trustworthy USB Drive
A USB drive is a common way for us to carry our data from one place to another. We can not eliminate USB drives' use because of their advantage of easy portability.
However, to prevent USB attacks, consider inserting only those USB drives that you completely trust. There is no need to plug any USB drive that you find. Make sure you trust the source through which you are getting the USB drive in the first place.
Tip 2: Separate Personal USB Drive from Work USB Drive
If you are using the same USB to carry your data and work-related data, you are at high risk of a USB attack. The reason can be because you may be plugging your USB into many other computers for personal or work reasons.
It can result in your USB drive contracting with any infected computer. Hence, your personal and work data are both highly vulnerable to hackers. So, I recommend keeping two separate USB drives for personal and work.
Tip 3: Create Safe USB Keys
If you wish to prevent your USB drive from getting infected, you can create safe USB keys. A Safe USB key allows you to put a key or password onto your USB drive. No one can access your USB drive without the key, and the files inside are encrypted.
You can create safe keys using external software, but you can also use BitLocker if you are a Windows user.
Tip 4: Use Qualified Antivirus Software
Since researchers have already identified almost 29 of the USB attacks, you can take the proactive approach. Using up-to-date antivirus software, you can detect all the commonly occurring USB attacks at once before they do any damage.
You can use some of the qualified antivirus software that are Avast, Kaspersky, and Norton 360.
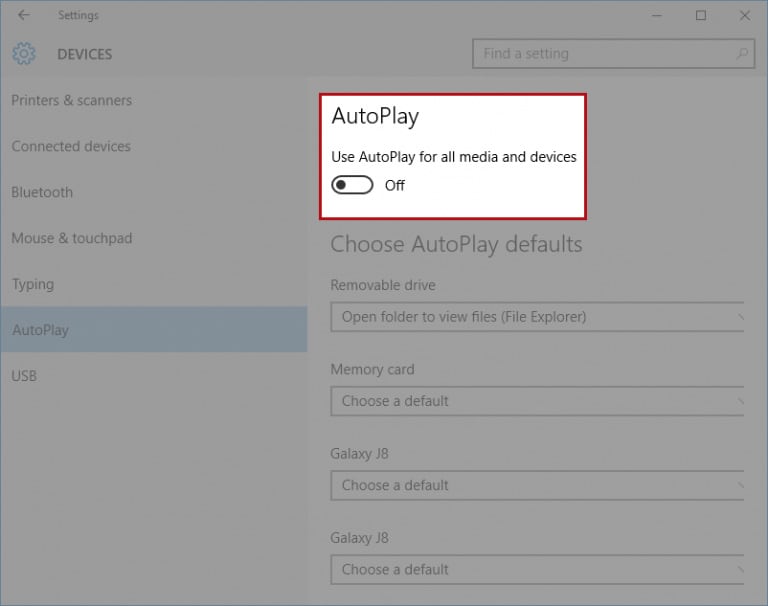
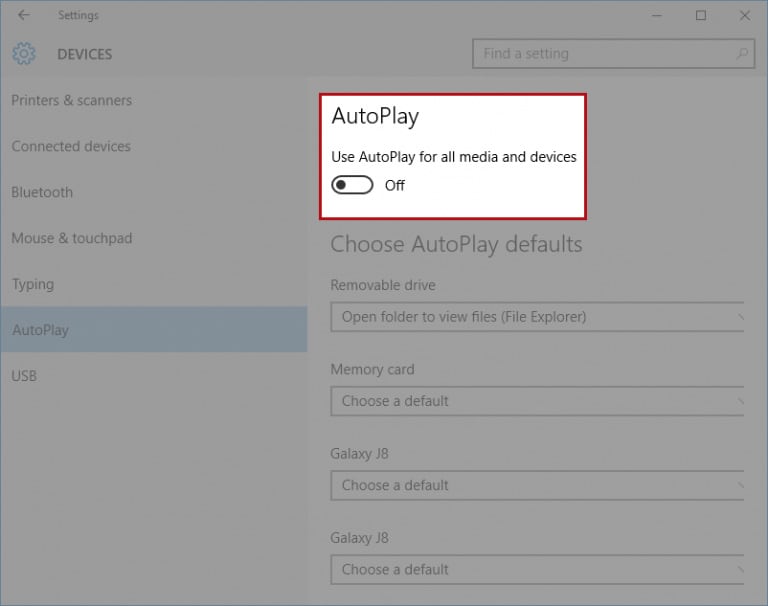
Tip 5: Disable Autorun Features on All Your Devices
Most of the time, a USB drive (even when plugged in) does not attack until infected files are executed. To prevent those files from execution, make sure to disable the autorun feature on your devices. It will ask you before running any file.
To disable autorun features in Windows 10, follow the below steps:
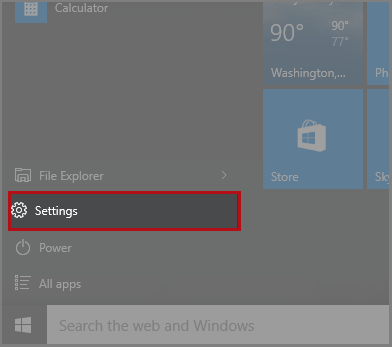
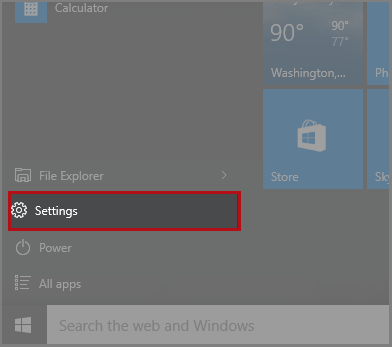
Step 01: Open Settings
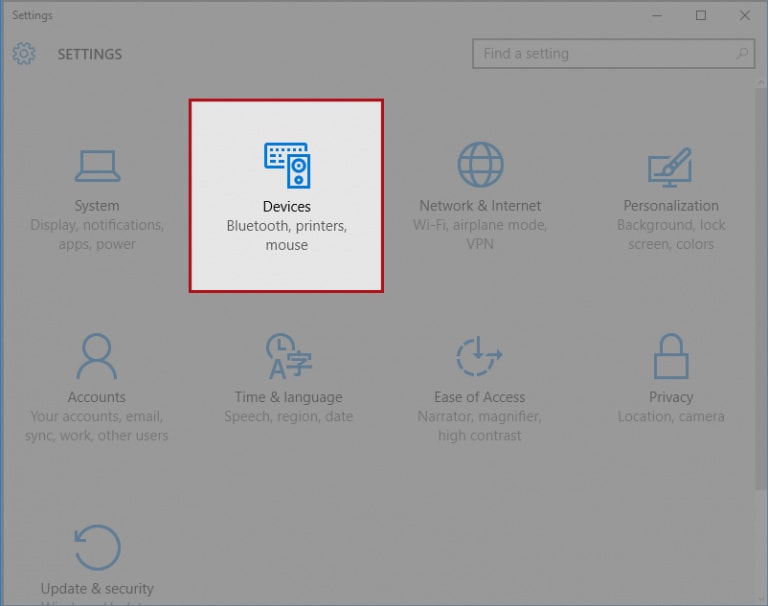
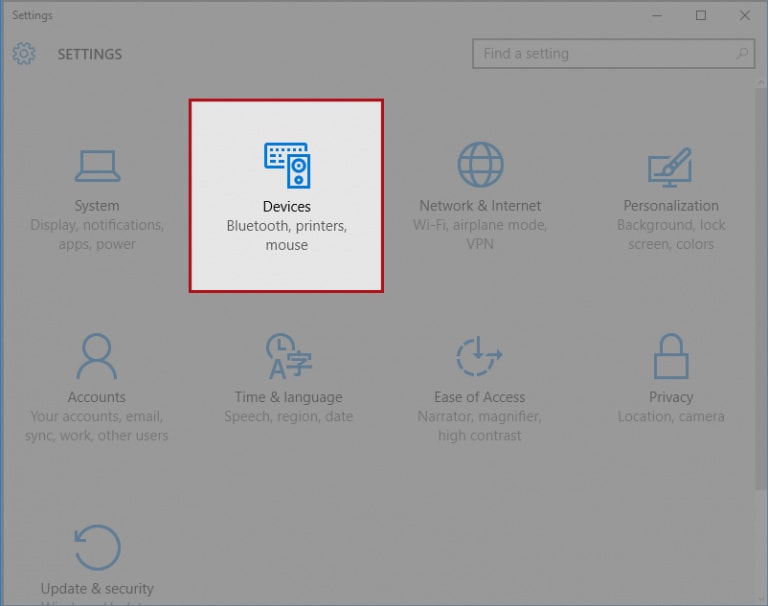
Step 02: Select Devices
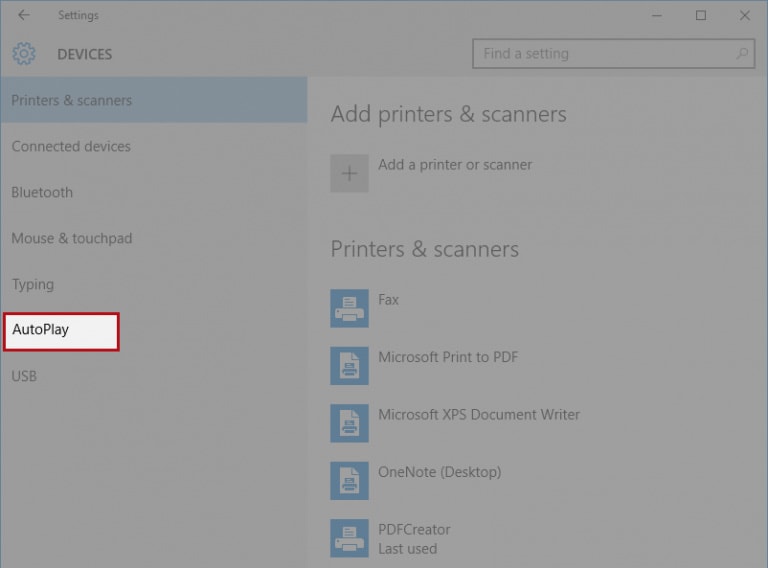
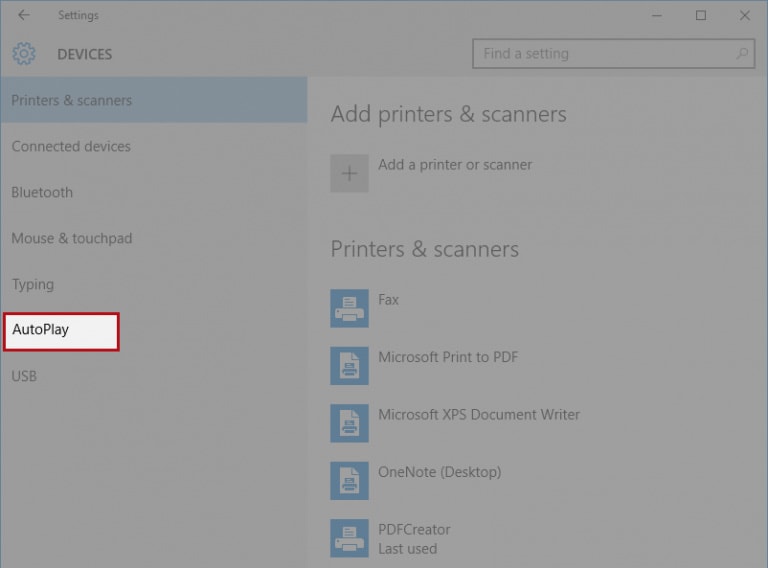
Step 03: Choose AutoPlay from Left Side Menu
Step 04: Turning Autoplay Off
Now you have learned 5 ways to prevent USB attack, let's look at how to recover data when USB attack causes data loss.
Part 03: What to Do When USB Attack Causes Data Loss?
If your USB drive has been attacked and the data inside has leaked, what would you do? Turn to manual service? That may coast you much. A good choice is to use third party software to help you recover your data. There are many data recovery tools, here I recommend Wondershare Recoverit for you.
Key Features
- Recover all types of data files.
- Allows file scan preview before recovery to fasten up the process.
- Filter files during the scan process.
- It helps you to create bootable media.
- It solves the blue screen death issue.
- It provides computer crash recovery.
- It repairs corrupt videos.
- Scanning video fragments.
- And many more!
Wondershare Recoverit Effectiveness for USB Data Loss
Suppose you have lost your data due to any attack. In that case, this Data Recovery software provides a feature for virus attack caused files recovery. You can download Recoverit and start its 3-step recovery right away!
If your lost files are no more than 100 MB, then you can recover them of any format for free if you download the free version.
Step 1: Select Your USB Location

With Recoverit Recovery Software, select the location from where you deleted your screenshots, and then click the "Start" button to begin the scanning process.
Step 2: Scan Your USB Drive

Recoverit lost recovery software will start scanning your selected hard disk to search deleted screenshots; scanning will take a while.
Step 3: Preview and Recover Deleted Data

After the deep scan, you can check all recoverable screenshots. You can preview the specific recoverable files, select your data, and click the "Recover" button to get them back.
Part 04: Conclusion
Now you have known that awareness of USB attacks is essential these days. Only with sufficient knowledge can one prevent USB attacks and the threats they bring with them.
Regardless of whether you are affected by any USB attack until now or not, it would be best to consider the tips we have shared. It is essential to disable the autorun feature and to have quality Antivirus software. One must also keep the basic safety guidelines in mind to play only those USB devices that are trustworthy.
Also, if you faced a USB attack, the possibility of losing data is high. So, whenever you face a data loss issue, I highly recommend Wondershare Recoverit software that is secure, reliable, and trusted by us.
USB Topic
- Recover USB Drive
- Format USB Drive
- Fix/Repair USB Drive
- Know USB Drive







 ChatGPT
ChatGPT
 Perplexity
Perplexity
 Google AI Mode
Google AI Mode
 Grok
Grok
























Eleanor Reed
staff Editor